Uncategorized
Streamline Your License Management with ServiceNow
Organizations often struggle to maintain a seamless license management. Mobiz is also…
What Is The NextGen Program For ServiceNow Implementation?
Did you know that ServiceNow implementation has successfully helped 6,300 individuals…
What Makes ServiceNow SecOps the Most Effective Security Platform?
As the digital world continues to shift at the speed of light, the kinds of attacks and…
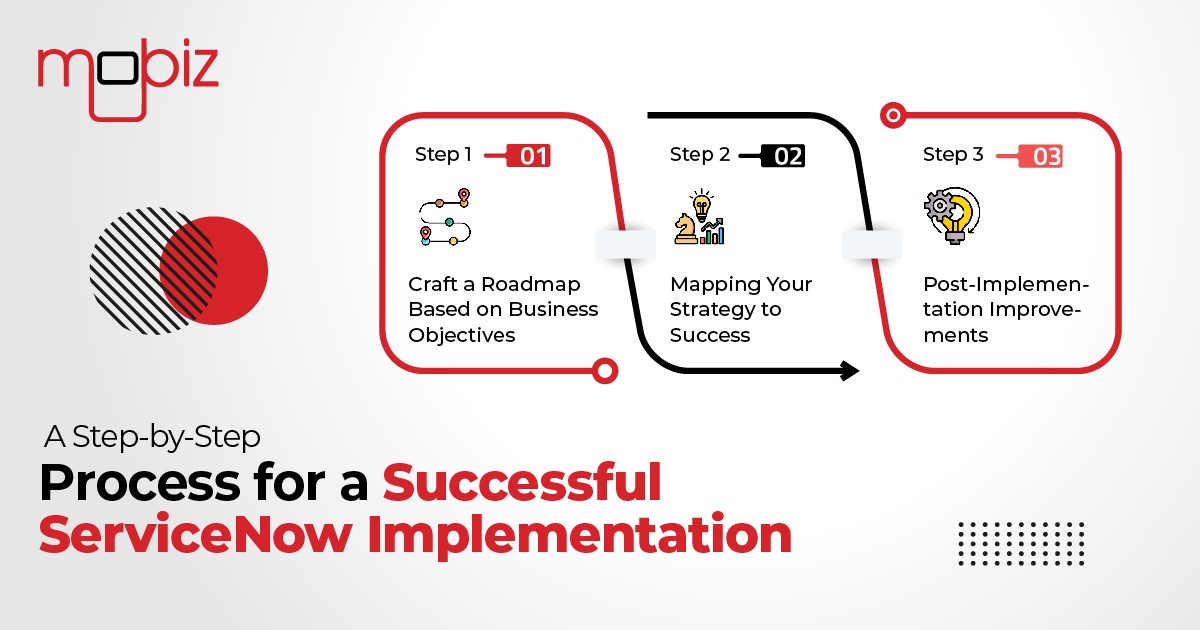
A Step-by-Step Process for a Successful ServiceNow Implementation
With its ability to define, deliver, and analyze services seamlessly, ServiceNow has…
How to do a ServiceNow Export to Excel: A Guide
ServiceNow export to Excel is an important process for businesses aiming to utilize their…
ServiceNow Predictive Intelligence: Do’s and Don’ts
In 2024, the buzz around AI is louder than ever. ServiceNow’s Predictive Intelligence is…
What Is Fileless Malware?
In an era dominated by digital connectivity, safeguarding your online presence is more…
What Is Ransomware Malware?
Do you find yourself wondering how ransomware works? In today's digital landscape,…
What Is Rootkit Malware?
The digital landscape is fraught with threats, and one of the most challenging is the…
Understanding Malware Delivery Methods: How Is Malware Spread?
Have you ever wondered how does malware get on your computer and how can malware be…